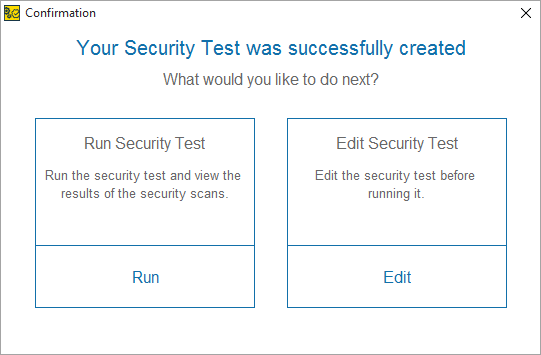
Private Security Business Startup: How to Start, Setup and Run Your Own Private Security Company (English Edition) eBook : Iqbal, Javed: Amazon.it: Kindle Store

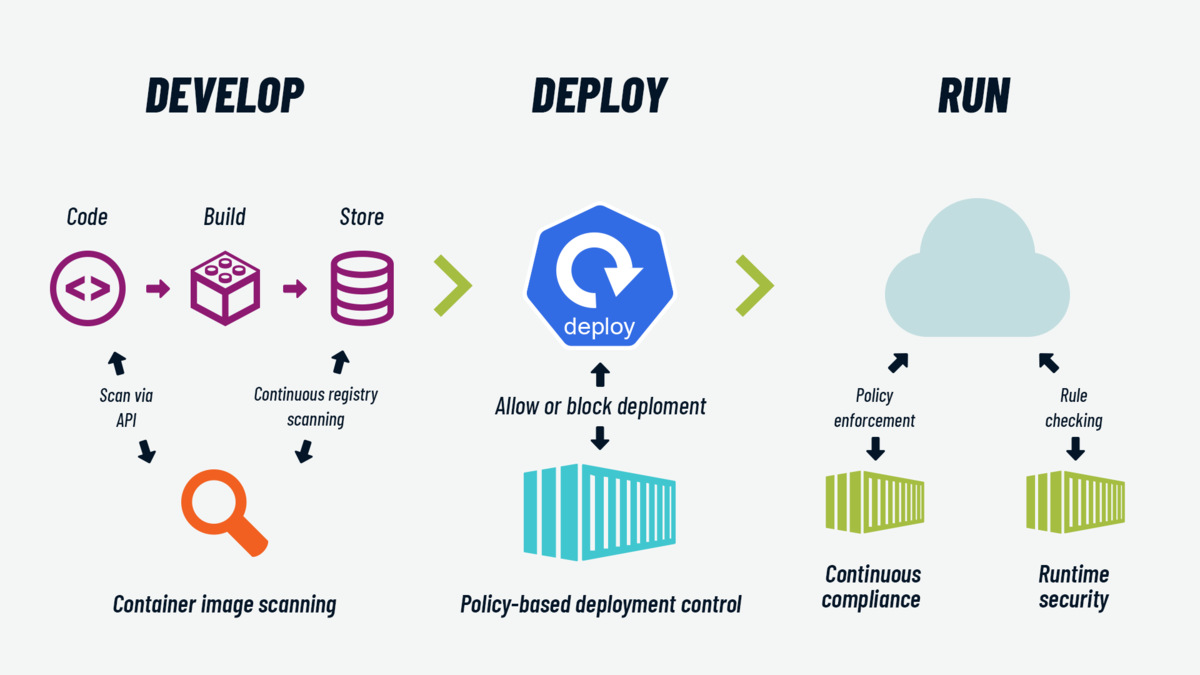
the agile admin | thoughts on agile web operations and devops by @ernestmueller, @wickett, @iteration1 and @bproverb